Privacy Coins vs Privacy Protocols
Privacy coins: awareness vs misunderstanding
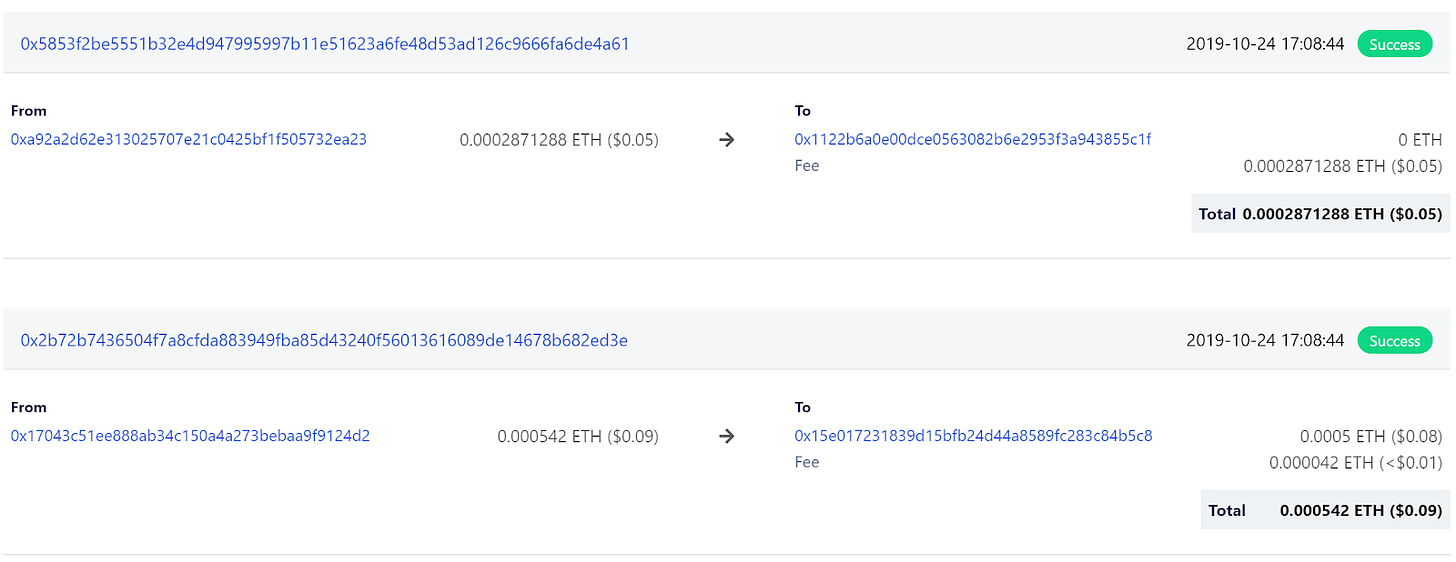
Bitcoin has brought the most transparent and secure record of accountable transactions, enabling the first practice of third-party accounting by a blockchain network ever. Some people say bitcoin is anonymous, in fact, it is the most transparent currency in the world, compared to cash and other kinds of money. Everyone can see details of a transaction on Bitcoin or Ethereum and many other public blockchains. For instance, Bob sends 1.5 ETH to Alice, and the network records as followed:
Transaction hash (ID)
Bob wallet address (sender)
Alice wallet address (recipient)
Bob sends an amount to Alice
Transaction fee 0.00104 ETH.
A transaction record on Ethereum Blockchain by Etherscan
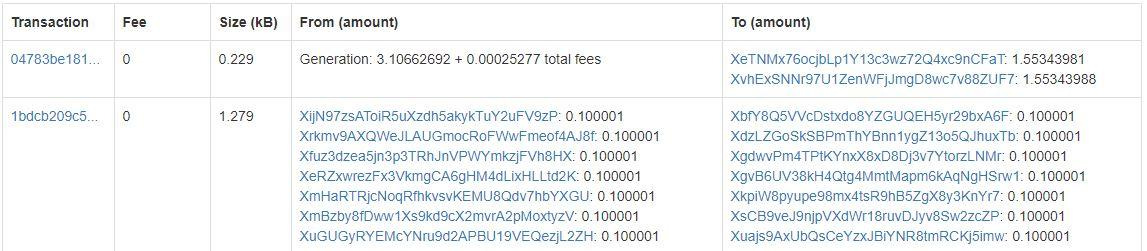
However, people don’t know who the actual owner of a Bitcoin or Ethereum address is. Because of transparency on the side of transaction tracking and anonymity on the side of address owner’s identity, popular blockchain transaction is considered to be pseudonymous. This, in several circumstances, is not a good solution. For example, in financial and banking transactions, account holders must be identified, while their transaction information is shown to authorized and involved parties only, not publicly exposed. That is why privacy coins are an interesting category in the cryptocurrency space. There are dozens of such coins. Several well-known ones include Monero (XMR), DASH, Zcash (ZEC), Komodo (KMD), Verge (XVG), GRIN, and BEAM. Blocks of those networks, basically, record all inputs (senders) and all outputs (receivers) but don’t specify their mapping, i.e. don’t clarify like from Bob to Alice.
A transaction record on Dash Blockchain by https://explorer.dash.org/
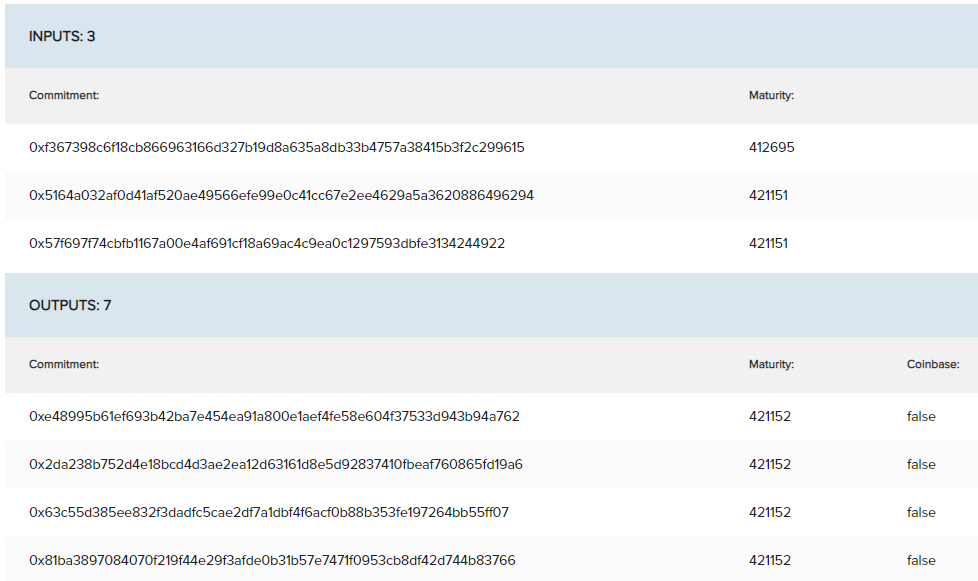
A transaction record on Beam Blockchain by https://explorer.beam.mw/
Basically, Beam records inputs, outputs, and kernels without any specific in between
Unfortunately, instead of developing protocols to fit the banking industry, the privacy coins intend to run out of government oversight and facilitate confidential transactions in money laundering activities and illicit financing. That is why several large exchanges have delisted Monero, Dash, and Zcash to comply with certain regulations.
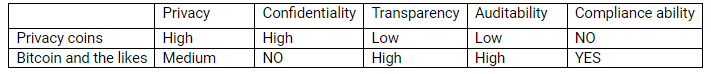
Privacy of transactions is a necessity of banking systems. On the other side, transparency is essential for accounting and audits. On public blockchains like Bitcoin and Ethereum, everything is transparent. Someone believes that it unsuits finance, health, and many others. It seems to have a trade-off (dilemma) in the blockchain: privacy vs transparency.
It should be distinguished as privacy vs confidentiality. Privacy ensures that transaction information is distributed to certain involved parties, not publicly available but can be shown to authorities per request. In contrast, confidentiality means that no one can know the full record of a transaction except the sender and the receiver, even some details may disappear forever some days. Obviously, a confidential transaction satisfies privacy but not vice versa. Banking and financial services need privacy and transparency but not confidentiality like what privacy coins offer.
How can bitcoin deal with the privacy vs transparency problem? It is implemented that all transactions on Bitcoin Network can be tracked and traced. Just one more simple step to complete. Whenever people want to buy or cash out bitcoin (or alternative coins) for fiat, they must access crypto-fiat exchanges or OTCs. Know Your Customer (KYC) is a simple procedure to comply with Anti-Money Laundering (AML) regulations. KYC allows exchanges to identify an individual to one or several Bitcoin addresses. Then, privacy is guaranteed by the firms while transparency is preserved. This is what Coinbase and other crypto exchanges have done for regulatory compliance.
Some authors argue that presently existing privacy coins should be renamed as “anonymous coins”. In practice, if a criminal wants to use GRIN or BEAM (or any others), he still needs to cash out somewhere. Therefore, fiat gateways are the bottleneck and/or barrier for money laundering. Together with low liquidity and harder regulations on crypto exchanges, anonymous coins are not a perfect mean for money laundering and illicit financing as desired.
Capability to support regulatory compliance (including AML) is a must for blockchains to get mass adoption. Zcash and Dash are going to develop protocols that enable privacy in an optional layer along with suitable tracking ability. A dark future is waiting for anonymous coins that fully support confidential transactions without traceability.
In the next, we will discuss extensively how blockchains solve the privacy vs transparency dilemma and available techniques to overcome the challenge.
Privacy protocols in the blockchain: an overview
We go through the development of privacy protocols and their implementation in the blockchain space. Privacy ensures that only certain people (the sender, the receiver, transaction verifier, record keeper, and authorities) are granted access to the transaction info, not public. Confidentiality means that no one can know transaction details except the sender and the receiver.
Note that complete transparency in Bitcoin has merits but exposing all transaction information to the public is not suitable for banking services and many other fields. Developers and researchers have addressed the issue and made some progress in privacy. Notable techniques can be mentioned here: Indistinguishability Obfuscation (IO), usage of homomorphic encryption, ZKPs, and ring signatures.
Indistinguishability Obfuscation is a beautiful cryptographic technique that can serve all privacy and confidentiality issues in the blockchain. IO allows for code obfuscation, which is a very ripe research topic in cryptography. It can make an unbreakable obfuscation mechanism that will turn smart contracts into a black box. The key idea behind IO is a multilinear jigsaw puzzle, which basically obfuscates program code by mixing it with random elements. If the program is run as intended, it will produce the expected output. Otherwise, it makes the program look random and garbage. However, the technology is not ready for implementation and deployment in practice.
Homomorphic encryption allows operations to be performed on encrypted data without knowing anything about it. Like IO, this technology is almost in theory. However, a significant advance of the concept has been implemented in the Enigma project by MIT's Media Lab. On blockchains, the technique enables processing on the ciphertext. For example, the data stored on the blockchain can be encrypted using homomorphic encryption and computations can be performed on that data without the need for decryption, thus providing privacy and confidentiality.
Zero-Knowledge Proofs (ZKPs) allow the prover to prove to the verifier that they know a value X without showing any information apart from X. To prove that one possesses knowledge of certain information, it is trivial to reveal it. The difficulty is to prove the possession without disclosing the information. A practical algorithm, Succinct Non-Interactive Argument of Knowledge (ZK-SNARK) has been implemented successfully in Zcash to ensure privacy. Ethereum's R&D team is collaborating with Zcash Company to integrate the protocol on Ethereum is already a very active research project being run. Another excellent paper is HERE. An additional ZKPs is Zero-Knowledge Succinct Transparent Argument of Knowledge (ZK-STARKs) which is an improvement on ZK-SNARKs. ZK-STARKs consume much less bandwidth and storage as compared to the formers. Also, they do not require the initial, somewhat controversial, trusted setup that is required for ZK-SNARKs. Moreover, ZK-STARKs are much quicker than ZK-SNARKs, since they do not make use of elliptic curves and rely on hashes. Another ZKP is Zero-Knowledge Prover and Verifier for Boolean Circuits (ZKBoo) but nowhere has been implemented yet.
Privacy protocols and techniques
State channels are a possible solution for privacy, available on the Hyperledger project. The idea relies on the fact that all transactions are off-chain and the main blockchain does not see the transaction at all except for the final state output, thus ensuring privacy and confidentiality. The original and full version of transaction info is stored at the channels (as side-chains).
Secure multiparty computation is based on the notion that data is split into multiple partitions between participating parties under a secret sharing mechanism. Then the network processes the data without the need of reconstructing data on a single machine. The computed output is shared between the parties as well.
Specific hardware can provide confidentiality to trusted computing platforms. For example, Intel Software Guard Extension (SGX) allows code to be run in a hardware-protected environment called an enclave. Once the code runs successfully in the isolated enclave, it can produce a proof called a quote that is attestable by Intel's cloud servers. However, people are concerned that trusting Intel causes a certain centralization that is not a true philosophy of blockchain. Nevertheless, many platforms have used Intel chips. On smart contracts then, once a node has executed the smart contract, it can produce the quote as proof of correct and successful execution and other nodes will only have to verify it. This idea can be further extended by using any Trusted Execution Environment (TEE) which can provide the same functionality as an enclave and is available even on mobile devices with Near Field Communication (NFC) and a secure element.
CoinJoin comes up with a simple idea that mixing transactions can produce privacy and confidentiality. The technique doesn’t map senders with receivers, instead, it concerns the total inputs and the total outputs to be equal without double-spending. Mixing results in a single address is no longer associated with transactions, which could lead to the identification of the users. CoinJoin needs interactive cooperation between multiple parties. Therefore, if anyone does not keep up with the commitment to create a single transaction by not signing the transaction as required, then it will result in a denial of service attack. In this protocol, there is no need for a single trusted third party. This concept is different from a mixing service which acts as a trusted intermediary among the bitcoin users agreeing with the shuffling of transactions.
Confidential transactions use Pedersen commitments that allow a user to commit to some value while keeping it secret with the capability of revealing it later. Two properties that need to be satisfied in order to design a commitment scheme are binding and hiding. Binding makes sure that the committer is unable to change the chosen value once committed, whereas the hiding property ensures that any adversary is unable to find the original value to which the committer made a commitment. Pedersen commitments also allow additional operations and preserve commutative property on the commitments, which makes it specifically useful for providing confidentiality in bitcoin transactions. In other words, it supports homomorphic encryption of values. Using commitment schemes allows the hiding of payment values in a bitcoin transaction. This concept is already implemented in the Elements Project.
MimbleWimble was introduced by an anonymous Bitcoin developer, namely Tom Elvis Jedusor (the French name of the fictional Harry Potter character, Voldemort). Mimblewimble is the name of a spell used to tongue-tie victims in Harry Potter as well. It extends the idea of confidential transactions and CoinJoin, which allows aggregation of transactions without requiring any interactivity. However, it is incompatible with the Bitcoin scripting language along with various other features of the standard Bitcoin protocol. Mimblewimble can enhance privacy and scalability issues both at once. Applying the technique results that a block containing an input list, output list, and something called excesses which are lists of signatures and differences between outputs and inputs. In contrast to Bitcoin, MimbleWimble outputs contain public keys only, and the difference between the old and new outputs is signed by all participants involved in the transactions. The protocol reduces block size while improving privacy and scalability. However, it is not suitable for accounting and banking services in general, since sender-receiver mapping and transaction amount are recorded nowhere. GRIN and BEAM have successfully implemented MimbleWimble.
Bulletproofs is a non-interactive Zero-knowledge Proof protocol for general Arithmetic Circuits with very short proofs (Arguments of Knowledge Systems) and without requiring a trusted setup. The essence of Bulletproofs is its inner-product algorithm, a proof (argument of knowledge) for two independent (not related) binding vector Pedersen Commitments that satisfies the given inner-product relation. Bulletproofs result in communication-efficient, zero-knowledge proofs, but reduces overall communication by a factor of three. Bulletproofs have a wide range of applications, for instance, in Multi-party Computation (MPC) systems, privacy protocols, and secret communications. An original Bulletproofs research is HERE.
Additionally, Monero has utilized ring confidential transactions (ringCT), stealth addresses, and ring signatures for privacy. However, those techniques increase the complexity and blocksize. Recently, Monero has been trying to implement Bulletproof, instead. Other confidential transaction techniques are provided by smart contracts.
Conclusion
There are a dozen privacy techniques out there. Many protocols are successfully implemented but some have not come into practice yet. Of course, privacy is a need for blockchain, but it should get along with security, scalability, transparency, and auditability. In the following, we summarize our discussion in a brief comparison regarding notable privacy protocols under several criteria. Due to a lack of knowledge and information, some are blank.
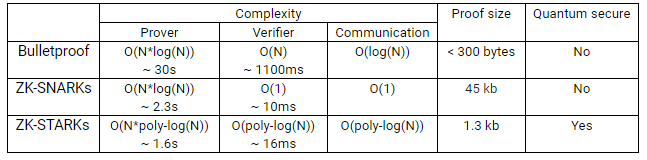
Algorithm comparison
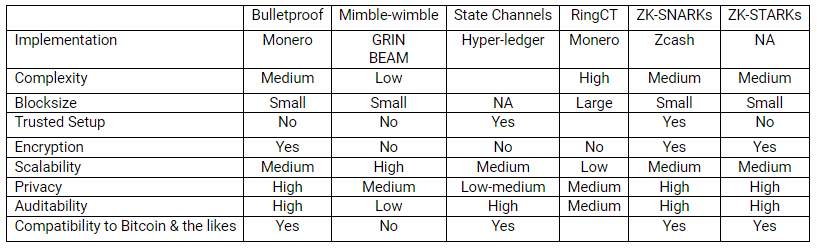
Protocol comparison
ZKPs are the most interesting techniques since they offer true privacy and confidentiality along with a wide range of applications in various fields. Compared to the aforementioned anonymous cryptos, Dash seems to be the most obsolete one, since it uses private-send (a kind of confidential transaction) with low privacy and scalability. Monero, after Bulletproof implementation, is going to be one of the two best privacy coins. The other is Zcash which has offered a multi-level of shielded transactions providing users many options to send their funds like Bitcoin or in a completely confidential way according to their wish. This brings Zcash to a better approach for compliance among the group. Note that Bitcoin, Ethereum, and many other cryptos are allowed in the U.S. and some other nations, classified as crypto-assets, but regulation is still the hardest challenge for anonymous coins.
Harmony team, in 2020, aims to develop a concept of “auditable privacy”. They don’t specify what auditability and privacy mean in their terms. However, they revealed that ZPKs (BulletProof) are investigated for implementation, attached with the confidential transaction and multi-level signature techniques. Incognito, on the other hand, is developing a decentralized platform for issuing privacy coins, based on the fundamentals of ZPKs, homomorphic encryption, ring signature, and confidential techniques. Some progress has been made. Nevertheless, privacy versus transparency (auditability/traceability) is naturally a tradeoff. Technically, making them balanced and scalable is difficult, and multiple privacy techniques are possibly incompatible and ineffective.
Privacy technology is an interesting and hot topic not only in the crypto space but also in blockchain, cloud computing, and data sharing. No one is perfect. No single technique is sufficient. However, the author analyzes various privacy techniques on different sides and criteria. Hope that this article can help developers choose what is suitable for their own blockchains or computing platforms.
-----
If You love the post, you may wish to donate for this special charity: https://www.carryforwardvietnam.org/donate/
Nếu bạn thích bài viết, bạn có thể đóng góp cho dự án từ thiện: https://www.carryforwardvietnam.org/donate/